On 11 march 2019 Ruckus networks achieved the FIPS 140-2 compliance level, more specifically level 2. For Ruckus as a hardware vendor this is a big deal because this means they can deploy Ruckus wireless technology for the US Federal Government. Since US Federal Government has strict requirements for technology this is a benefit also for them, they have more options now in picking a hardware vendor for wireless projects.
If we look into this FIPS 140-2 certification it is import to know this certification has 4 levels of security starting from level 1 as the lowest and level 4 as the highest. Ruckus Networks is now compliant with level 2 security, the hardware has some physical security mechanisms as tamper-evident coatings or seals that must be broken to get phycial access to the cryptographic keys.

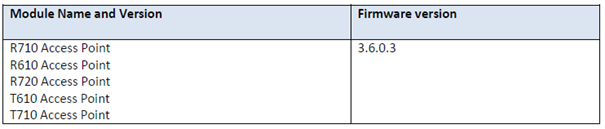
According to the FIPS 140-2 compliancy, deployments for US Federal Government can only be performed with the hardware tested on that specific firmware version. Other software versions or upgrades
What is in fact being tested before compliancy status can be granted ? Before an access point can communicate with the WLAN controller, the controller has to approve the access point as a trusted node. The access points on their end provide an encryption service between themselves and the wireless clients. The management traffic between the Ruckus access point and the controller is also encrypted using 128bit AES SSH. All master, public and private keys are stored in plaintext in the RAM of the hardware. For instance the EAPOL MIC key to perform integrity validation for 4-way handshake and the PMK to derive PTK are stored all in RAM. Passwords for user authentication , SSH RSA public and private keys, WPA2 PSK for client authention are all stored in RAM but also in the flash in plaintext on the hardware.
This is why the hardware needs tamper protection seals to verify no one can get physical access to these modules in the AP’s.
The FIPS 140-2 compliancy also checks the self-test procedures for the module during power-up and conditional self-tests. For each individual algorithm there will be some KAT tests to check the modules, key hashing and cryptographic algorithms will be tested. The KAT test stands for Known-answer Test.
A known-answer test involves operating the cryptographic algorithm on data for which the correct output is already known and comparing the calculated output with the previously generated output (the known answer). If the calculated output does not equal the known answer, the known-answer test willfail.
Although FIPS 140-2 is a good thing it is a continuous process to keep in line with the current security protocols and cryptographic algorithms. Once WPA3 will be available a new 192-bit security level is required to deploy WPA3-Entreprice networks based on NSA’s Suite B. Ruckus hardware will have to be tested against these new security levels and achieve the compliancy level again for new deployments.